When Agents Diverge from Reality: Implementing Runtime Guards
Bridging the gap between design-time logic and runtime physics || Edition 28
This post is part 10 of the Agentic AI Series — a multi-part exploration of how autonomous systems are reshaping enterprise architecture, governance, and security.
The Mechanics of Mismatch
In January 2025, Acme logistics ran an agent fleet that processed shipping updates across 12 warehouses. Each agent had the full set of design-time controls for validation rules, retry logic, and execution budgets.
The incident started with a timeout–latency mismatch between the orchestrator and a supplier status API. The orchestrator timed out requests at 30 seconds. During a period of latency, the supplier frequently completed successfully at roughly 35 seconds.
At 30 seconds, the orchestrator classified the call as failed and triggered downstream handling (cancellation and compensation). A few seconds later, the supplier’s success response arrived, but the system had already moved on.
This created two conflicting states for the same transaction:
Internal system: Marked as failed → triggered 2,400 cancelled shipments.
External reality: Succeeded → shipments were processed and shipped by the warehouse.
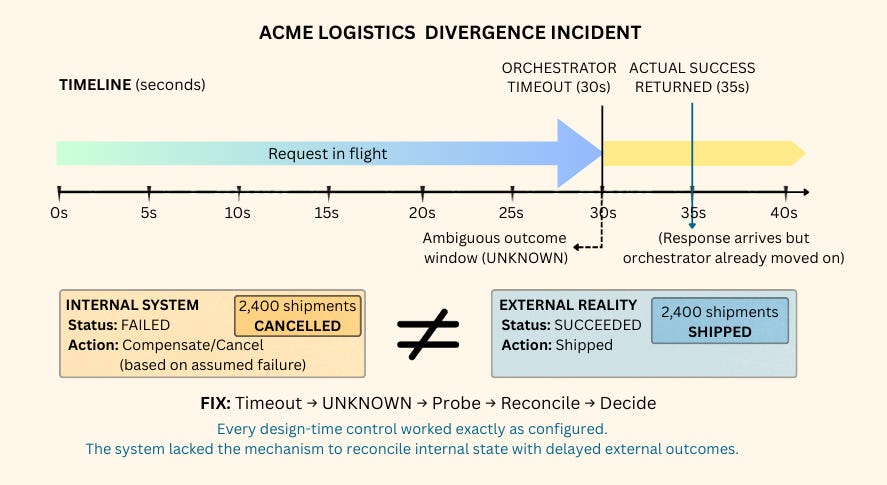
The result: major operational rework. Teams had to manually reconcile records, unwind incorrect cancellations, and work to restore trust in the automation layer.
What should have happened at 30 seconds was a third outcome state: UNKNOWN.
A timeout is missing evidence, so the system should pause irreversible automation until it can confirm the external outcome.
The system lacked a mechanism to reconcile internal state with delayed external outcomes. This gap between assumed failure and actual execution is exactly why runtime guards are necessary.
The Short Version
Production creates ambiguity. Latency, retries, and timeouts break the clean binary of “success vs. failure.” Agents need a runtime layer that can pause, probe, or degrade gracefully without guessing.
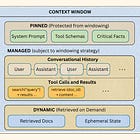
Guards decouple correctness from reasoning. Critical boundaries—flow control, truth maintenance, security posture, governance enforcement—must be enforced by the runtime environment, not by the agent’s prompt or logic.
The UNKNOWN state is critical. To prevent state divergence, systems must treat timeouts as
UNKNOWN, triggering aprobe → reconcile → decideloop before taking irreversible action.Guardability is a launch gate. Before shipping, teams must answer: How do we stop it? How do we confirm outcomes? How do we prevent cascades? How is authority scoped? And how is behavior audit-proven?
Governance must hold under pressure. Policies are implemented as machine-evaluated constraints. When enforced at the execution boundary, governance becomes consistent, blockable, and auditable.
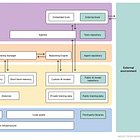
From Design to Operations
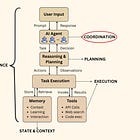
Design-time controls define what the system should do when everything behaves. Runtime guards manage what the system does when execution meets latency, contention, and partial failure.
Design-time controls answer “Is this action allowed?” through specifications, schemas, and tool contracts. Runtime guards answer “Is it safe to execute right now?” by controlling timeouts, retries, concurrency, stop paths, and reconciliation when outcomes are uncertain.
Incident Anatomy: How Failure Compounds
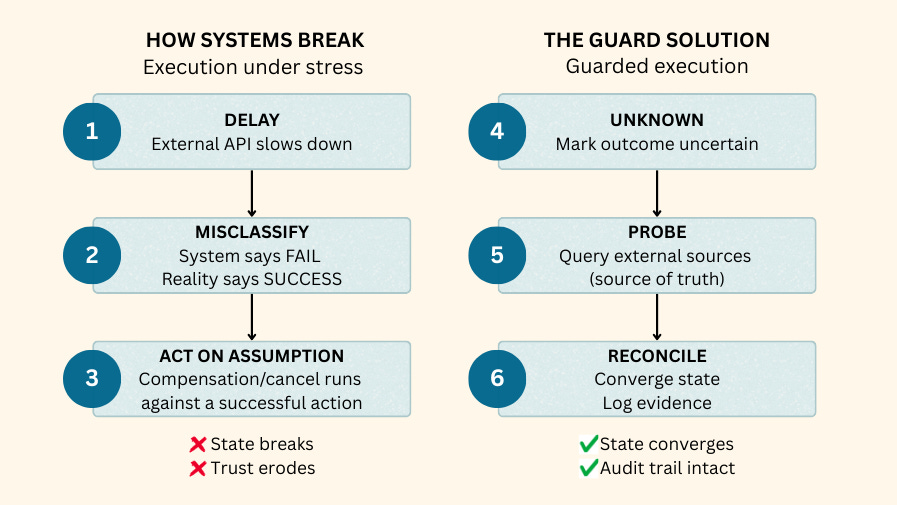
The logistics story earlier in this post follows a predictable pattern: latency increases, a timeout gets treated as failure, and downstream actions run against an outcome that actually succeeded. That chain—delay → misclassification → action on assumption—is how divergence forms and why “success/fail” breaks down in production.
The guarded path replaces guessing with reconciliation: treat timeouts as UNKNOWN, probe the external source of truth, reconcile state, and log evidence before taking irreversible action. The sections below break down the runtime guard categories that enforce this behavior under load.
Guards, by Failure Surface
These categories cover the failure surfaces that appear most often in production agent systems.
I. Flow Control
Prevent runtime failures from turning into cascades by regulating concurrency, retries, and throughput under load.
Flow control guards prevent execution from amplifying its own failures. They define when execution should proceed, slow down, or stop when dependencies degrade or resources are contended.
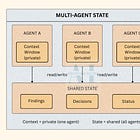
1. Concurrency & Locking
Ensures only one agent can mutate a given resource (order, ticket, document, account) at a time.
Without it: Concurrent plans can interleave writes and overwrite each other, producing inconsistent state that no single agent intended.
At runtime: It’s enforced at the
intent → actionboundary using resource locks, optimistic version checks, or single-flight execution for identical mutations, forcing other attempts to wait, retry, or abort.The Check: Can two agents mutate the same resource without coordination?
2. Circuit Breakers
Stops cascading failures by detecting dependency degradation and failing fast rather than compounding load.
Without them: Retries stack, latency spreads, and localized slowdowns consume the entire system.
At runtime: They enforce a state machine—closed (normal), open (fail fast), half-open (controlled probing)—that trips when error rates, latency, or volume cross thresholds.
The Check: When a dependency fails, do requests fail fast or retry indefinitely?
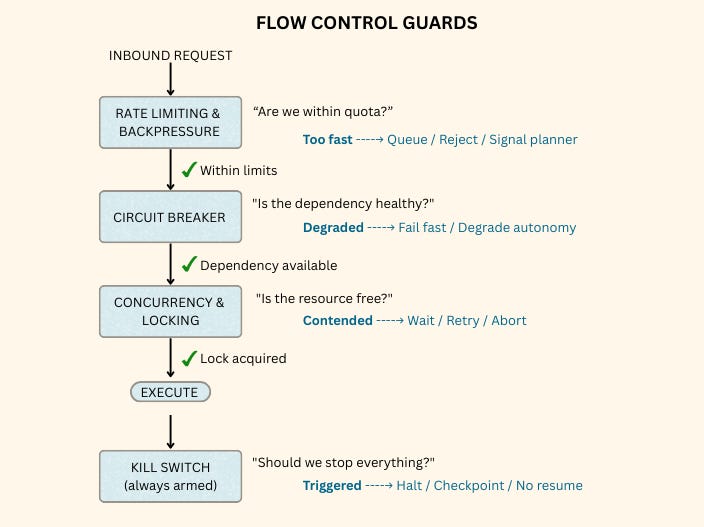
3. Rate Limiting & Backpressure
Regulates how fast agents are allowed to act, preventing quota exhaustion and cliff failures.
Without them: Scaling agents can overwhelm APIs, trigger provider bans, and lose capability suddenly rather than degrading gracefully.
At runtime: They’re enforced through per-tool and per-tenant quotas, queue limits, and explicit backpressure signals exposed to the planner so agents adjust behavior before hitting limits.
The Check: Do agents learn about capacity through signals, or by discovering failures?
4. Kill Switch
Provides fast, deterministic human override when automated controls are insufficient and outcomes become unacceptable.
Without it: Stopping harm in progress requires a deployment or configuration change—too slow when regulatory exposure, customer harm, or runaway automation is underway.
At runtime: It’s wired directly into orchestration with support for global or scoped shutdowns, measured time-to-halt, and explicit recovery paths that prevent auto-resume.
The Check: Can you halt execution in under 60 seconds without deploying code?
II. Truth Maintenance
Ensures internal state reflects what actually happened in external systems.
These guards exist because distributed execution produces delayed, partial, or ambiguous outcomes. They define how execution pauses, probes external sources, and reconciles state before downstream actions proceed.
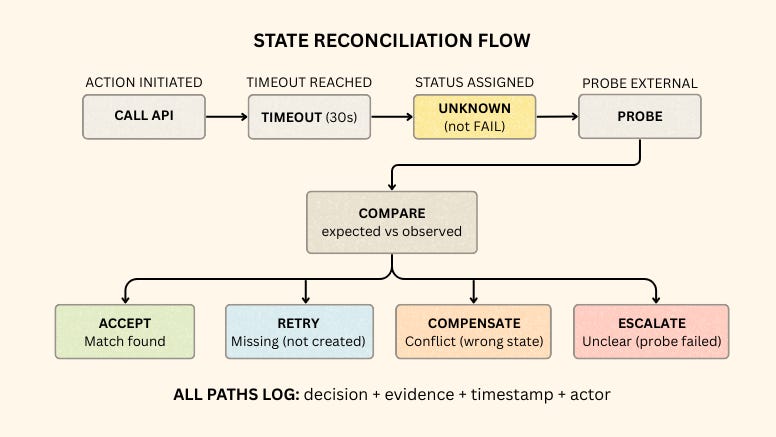
5. State Reconciliation
Handles ambiguous outcomes by treating timeout as “unknown” rather than “failed,” then probing to determine what actually happened.
Without it: Systems act on assumptions—triggering compensation against actions that actually succeeded, or retrying actions that already completed.
At runtime: It enforces a sequence:
timeout → mark UNKNOWN → probe external system → compare expected vs observed → decide(accept, retry, compensate, or escalate). Probing can be passive (listen for late webhooks), active (query status endpoints), correlated (reconstruct from logs and trace IDs), or escalated to humans when automation can’t resolve.The Check: When an action times out but succeeds externally, do you detect and converge—or do you diverge?
III. Security Posture
Prevents routine automation from turning into uncontrolled authority during execution.
These guards limit blast radius by controlling how credentials are issued, scoped, and revoked. They treat tool identities with the same rigor as human identities: least privilege, short TTLs, and rapid revocation when behavior deviates from expectations.
6. Identity Lifecycle
Prevents long-lived credentials from becoming permanent attack vectors by enforcing least privilege, short TTLs, and rapid revocation for every tool identity.
Without it: A single compromised credential—leaked in logs, exposed in misconfigured storage, or harvested through supply chain attack—grants broad, durable access to everything that credential could reach.
At runtime: It’s enforced through per-tool identities scoped to minimum required permissions, token TTLs measured in hours, automated rotation, immediate revocation pathways, and anomaly detection on usage patterns.
The Check: If one credential is compromised, how many systems can it reach—and how fast can you revoke it?
IV. Governance Enforcement
Turns business rules into executable constraints evaluated before actions run.
These guards prevent policy from being bypassed at runtime. They enforce business, risk, and compliance rules at the execution boundary, because only machine-enforced checks can block actions in production.
7. Policy-as-code
Enforces business, risk, and compliance rules as machine-evaluated constraints before execution, not documentation.
Without it: A request can be structurally valid—passing schema checks—while violating rules about jurisdiction, authority, or risk tolerance that exist only in wikis or tribal knowledge.
At runtime: It’s enforced after schema validation and before execution, with rejections that name the specific rule ID and reason, and evidence logged for audit.
The Check: Are business rules machine-enforced at the boundary—or treated as tribal knowledge?
Enterprise Governance & Accountability
Guardability Review
Before shipping high-impact workflows, answer five questions:
Invariants: What outcomes must the system never produce, even under stress?
Ambiguity: Where can timeouts or partial failures create UNKNOWN states?
Stop: How fast can you halt execution without deploying code, and who triggers it?
Reconciliation: How does the system probe and converge when outcomes are uncertain?
Evidence: Can you reconstruct intent → decisions → outcomes from structured logs?
Solid on three or four means normal failures are survivable but edge cases will hurt; fewer than three means hardening before real load.
Accountability by Role
If you’re building agents (Engineers, ML teams)
Instrument the seven verification questions as pre-launch gates
Design for UNKNOWN states explicitly—never assume binary success/fail
Test misalignment scenarios: orchestrator timeout vs dependency p95 latency
If you’re managing agent programs (Product Managers, Delivery Leads)
Include guardability review in workflow approval process
Track scorecard metrics across workflows; flag regressions
Schedule quarterly game days: dependency failures, rate limit exhaustion, credential revocation
If you’re governing agent systems (Security, Risk, Compliance)
Require minimum scorecard thresholds before production approval
Audit reconciliation logs for divergence patterns
Map credential blast radius per tool; enforce TTL policies
In Closing
Production failures rarely involve a single breakdown. They emerge from interactions under pressure—timeouts, retries, concurrency, and ambiguous outcomes amplifying each other. Runtime guards turn those failure modes into bounded behaviors: degrade, stop, reconcile, and recover with evidence.
The next post moves up a layer: Autonomy Policy—how enterprises grant authority by risk tier, how systems downgrade safely when guarantees are missing, and how to keep fallback governance from becoming its own attack surface.